Managed Security has never been static. In almost 25 years I’ve built Managed Security at Optiv, run it at MDRs such as Expel, ran architecture teams and enablement for MSSPs globally at McAfee, and spent time at vendors with solutions to support the maturity in the industry. But the pace of change we’re experiencing right now is unlike anything I’ve seen in my career building and operating MSSP and MDR providers.
For years, success in managed security was defined by scale: more alerts processed, more endpoints covered, faster mean time to acknowledge. Today, that definition is fundamentally broken. Customers expect more context, more proactive defense, and more measurable outcomes. On the other hand security teams face staffing shortages, tool sprawl, and accelerating threat complexity. Over the years I’ve chased new promises of a silver bullet, of the latest shiny object that would ‘solve’ the problem for my teams. Alas, I was disappointed more times than not. The issue I’ve always had to confront was that most tools are built to solve problems that were defined by the builder; while most problems faced by customers are nuanced and ever evolving. Most of the time the tools were too static and rigid, or they were infinitely configurable provided you had never-ending time and resources to manage them. I can feel a lot of you shaking your heads right now because you feel my pain. Thank you 😀
This is the backdrop against which agentic AI has entered the managed security conversation. And it’s forcing the industry to confront some hard truths about how we’ve been operating.
From Manual Workflows to Fragile Automation
The early evolution of managed security was manual by necessity. Analysts triaged alerts, followed playbooks, pivoted between tools, and documented findings by hand. Automation promised relief and delivered, sort of. During these early years I learned that good SOC analysts had a ‘half-life’, and you knew that a plan was necessary to manage the inevitable burn out over time.
We moved from manual workflows to chained automations with hard dependencies: SOAR playbooks, scripted enrichments, decision trees. These systems helped teams move faster, but they were brittle by design. Any deviation in inputs, any change in a customer environment, any new data source could break the workflow or force costly re-engineering. I once spent a year working to deploy SOAR in an MSSP infrastructure only to find out you never finish. Even if you do make the investment in time and energy to build robust use cases that deliver results to the SOC analysts, more often than not you’ve just transferred the problem to the engineering team who are overwhelmed. It’s exhausting.
Modern security teams don’t operate in static environments. They manage dynamic cloud infrastructures, hybrid identity systems, and constantly evolving threat landscapes. Automation that assumes a fixed path just doesn’t cut it.
Managed Security Customers Expect More … Much More
And, surprise (in my best sarcastic voice), customer expectations have expanded dramatically.
Alert triage and investigation are now table stakes. Today’s managed security customers expect:
- Continuous threat hunting, not just reactive response
- Threat intelligence correlation across telemetry, behavior, and external sources
- High-quality reporting that speaks to both operators and executives
- Custom detections, procedures, and response actions aligned to their business
- Support for evolving use cases that didn’t exist when the contract was signed
They expect a security partner, not an alert factory.
For MSSPs and MDRs, this creates a tension: how do you (or even can you) deliver deeply customized outcomes across many customers without exploding costs or operational complexity?
The Vendor-Defined Problem Trap
Many vendors are attempting to solve this challenge by tightly defining “the problem” and then building AI agents designed to solve that specific slice, AISOC, Threat Hunting, Attack Surface Management, Phishing analysis, and so on.
The issue is that real customer problems rarely fit neatly into vendor-defined boxes. Even less want to have to purchase a myriad of tools from different vendors to be able to implement a holistic AI strategy.
Every organization has its own data sources, risk tolerance, regulatory pressures, and operational quirks. When AI solutions force customers to adapt their workflows to the tool, rather than the other way around, friction happens. The result is partial adoption, workarounds, and more tools that security teams have to manage. When you’re creating new problems to try and address the existing one it’s like moving the food around on your plate instead of eating … you never finish or feel satisfied.
Agentic AI Requires a Platform Mindset
True agentic AI platforms take a fundamentally different approach.
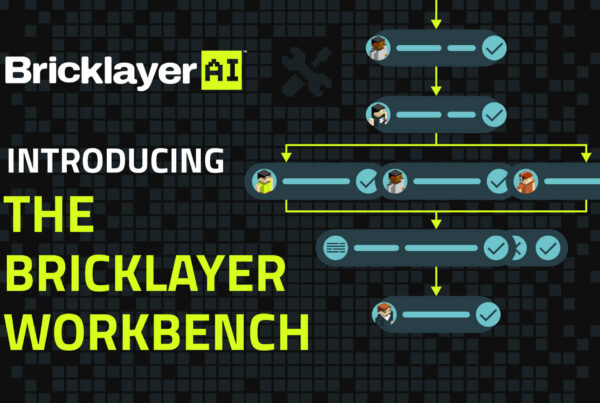
Rather than delivering a single monolithic agent, platforms like Bricklayer embrace a distributed agent workforce model. Each agent is purpose-built, specialized, and scoped to a specific task that include enrichment, correlation, investigation, response, reporting, or customer-specific logic.
Critically, customers aren’t limited to pre-defined agents. They can build additional customized agents and procedures that reflect their version of common use cases, or entirely new ones. No rigid boxes. No forced workflows.
This matters enormously in managed security, where providers must balance consistency with customization across dozens or hundreds of customers.
The Power of Collaborative Agents
Distributed, collaborative agents also unlock real advantages in accuracy and governance.
When agents work together, each validating, enriching, or refining outputs, the quality of results improves. Errors are surfaced earlier. Assumptions are challenged. Context is preserved. It works like a human team would IF they had the time to continuously collaborate and reach consensus.
Just as important, access can be tightly constrained. Each agent only sees what it needs to do its job. This principle of least privilege isn’t just a security best practice, it’s a requirement when AI systems are operating across sensitive customer environments.
Transparency Builds Trust
One of the biggest barriers to AI adoption in managed security is trust.
Security operators need to know what work is being done, why decisions are made, and how conclusions are reached. Black-box AI erodes confidence and increases risk.
Agentic platforms must provide task-level transparency: clear visibility into every action taken by an AI agent, the data it used, and the outcome it produced. When operators can review, validate, and learn from AI-driven work, trust follows, and results are consistently delivered.
Scale Without Engineering Bottlenecks
For MSSPs and MDRs, flexibility is meaningless if it requires custom engineering for every new customer or use case.
A true platform enables teams to build and adapt workflows, agents, and procedures without specialized coding or engineering effort. This is essential when managing multiple customers with diverse needs, compliance requirements, and threat profiles.
The ability to rapidly create new use cases and evolve them over time is no longer a “nice to have.” It’s central to the managed security business model. Just as important is that your tools provides common templates and OOTB solutions to jump start your efforts and quickly get you to baseline results without limiting your ability to iterate over time.
Avoiding the Next Wave of Tool Sprawl
Finally, there’s a strategic risk the industry must address head-on. I’ve been a part of organizations aligned to the ‘in a box’ solutions where the provider brings the infrastructure. It suits some but is limiting for larger, more complex organizations. I’ve also built organizations focused on co-management, where expertise in SecOps is the real value is highly resource dependent across a wide variety of technologies. It simply doesn’t scale over time.
Vendors focused on solving a single problem with AI, without a broader platform vision, are setting customers up for the next generation of tool sprawl. One AI for AISOC. Another for case management. Another for reporting. Each with its own data model, permissions, and governance challenges.
Without a unifying platform, operational coherence breaks down and security teams are left stitching together disconnected intelligence.
Agentic AI, done right, isn’t about replacing analysts or chasing the latest acronym. It’s about building a transparent, collaborative foundation that evolves with both threats and customer expectations. It brings humans into the loop at the times when they are needed to provide intuition and nuanced thinking to validate the heaving lifting done by AI. Mechanizing the assembly line, done decades ago with a lot of angst, created new opportunities for more meaningful work. In many ways, the SOC analyst was forced into the role of the assembly line worker in SecOps. Agentic AI designed from day one as a platform provides a similar opportunity because you aren’t learning to use a tool, but are given a toolbox.
Managed Security has entered a new era. The providers and platforms that succeed will be the ones that recognize agentic AI not as a feature, but as a new operating model. For the first time in over 2 decades I see the capability of technology converging successfully with the vision. Welcome to 2026!